In this article:
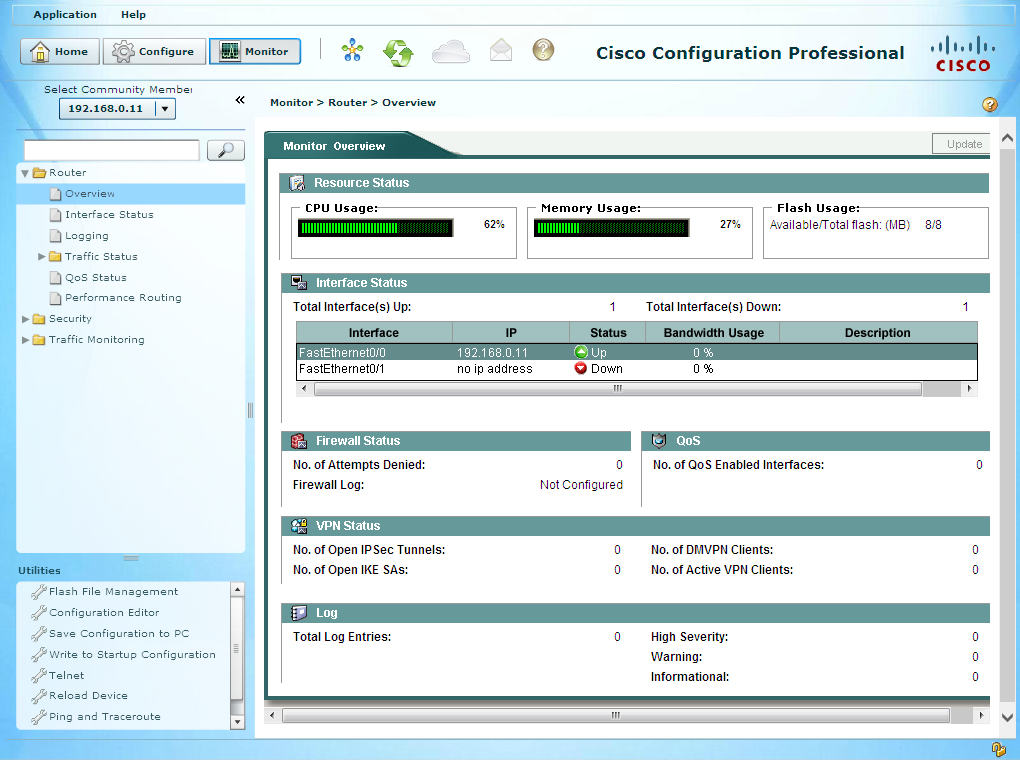
The Cisco Configuration Professional (CCP) is a graphical interface allowing to quickly and easily configure, monitor and troubleshoot Cisco IOS-based devices. It does exactly the same thing as one could do using IOS command-line, but using more convenient graphical tools and optional wizards for multi-steps configuration, including operations involving several devices like setting-up a tunnel.
It comes in two versions:
-
CCP 2.x, also known as Router and Security Device Manager Software (SDM), it is the little brother of ASDM used to configure ASA firewalls. This is a desktop application, the GUI is installed locally on the user’s host.
-
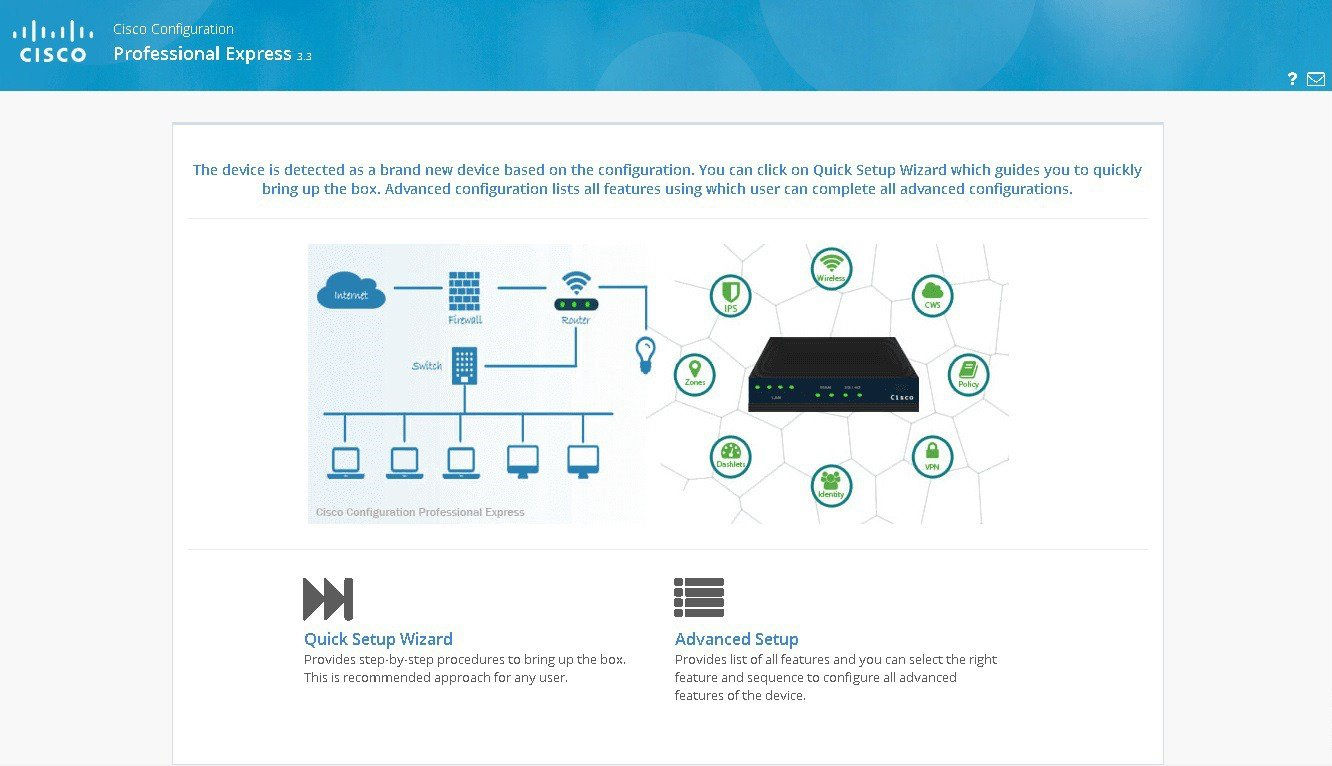
CCP “Express” 3.x: this version is deployed on the Cisco devices themselves and leverage devices’ HTTP port to embed a web configuration interface. CCP Express already existed in the 2.x generation, at that time two flavors were available: the “end-user” one with reduced functionalities (the end-result was very similar to home Internet boxes) and the “administrator” one. The current 3.x version only takes over the “administrator” version.
Note
For people training for the CCNA-Security certification, as of writing this post, being comfortable in using CCP 2.x is mandatory.
As far as I know, CCP Express 3.x however is out-of-scope.
CCP is freely downloadable from Cisco website (you only need to register).
CCP 2.x (Cisco SDM)
Prerequisites and installation
The latest version currently available is 2.5 and has been published in 2008. Yet it is still part of the CCNA-Security curriculum as per Cisco’s CCNA-Security official cert guide which describes its use in details (but do not cover the deployment).
Now comes the time to check you are well sited. If your chair is equipped with a sit-belt, make use of it. If there is any children in the room, please keep them away. Ah, and let’s add one of those nice red banners too:
Advisory
Gory details follow!
Still with me? Okay. CCP 2.x installation and use is quite straightforward as soon as you have all the prerequisites right. I warn you that they are just totally insane, they make my eyes bleed each time I look at them:
- I recommend using Windows 7: maybe it works on other system but I did not try it.
- You must use Internet Explorer (no Chrome, Firefox, Edge or whatever).
- On IE, you must enable the Compatibility View mode for the host 127.0.0.1 (you can find IE’s Compatibility View option below the Tools option in the menu-bar, press the Alt key to display the menu-bar)
- You must install the Adobe Flash Player for IE (no particular prerequisite on Flash Player version, the latest should be fine).
- You must use the obsolete and unsupported Java 1.6 (don’t try any newer version, it won’t work), use the 32 bits version even on 64 bits systems as this is usually the only one supported by browsers. Old Java releases can be found in the Java Archives page, the binary I’m using is named jre-6u45-windows-i586.exe.
- In Java properties (usually accessible through either an icon in the
notification bar or an icon in Windows Control Panel), add the parameter
-Xmx512mto increase the Heap Memory size allocatable by CCP as the default is too low. - If you are using the EMET security tool, disable or uninstall it as it interferes with CCP processing.
- Once CCP has been installed, copy its shortcut on your desktop and in its Advanced properties tick the checkbox to make it always run with the local Administrator privileges.
So, to summarize, CCP is a simple GUI sending TCP requests to remote IOS devices, and to do this it requires both Flash and an obsolete version of Java, disabling security features on the browser and on the system, and be run as administrator. “Security Device Manager” they call it, yeah!
Once you satisfy all prerequisites, the installation is straightforward.
Devices preparation
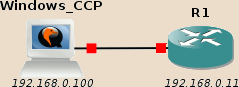
First, connect the Windows host running CCP to a device to configure, here a router:
Note
A VM node must be shut down to be able to edit its network links.
If you want to be gain more flexibility, just add a basic GNS3 switch between the Windows host and the router: you won’t need to shutdown the Windows host anymore when changing the devices connected to the switch.
CCP requires both a command-line and HTTP(S) access to the device. After having configured the network interface, you must create an account and start the HTTP service.
Here is the typescript showing a quick device configuration:
R1#conf t Enter configuration commands, one per line. End with CNTL/Z. R1(config)#int fa0/0 R1(config-if)#ip add 192.168.0.11 255.255.255.0 R1(config-if)#no shut R1(config-if)# *Mar 1 00:01:09.039: %LINK-3-UPDOWN: Interface FastEthernet0/0, changed state to up *Mar 1 00:01:10.039: %LINEPROTO-5-UPDOWN: Line protocol on Interface FastEthernet0/0, changed state to up R1(config-if)#exit R1(config)#username admin privilege 15 secret Cisco123 R1(config)#ip http secure-server % Generating 1024 bit RSA keys, keys will be non-exportable...[OK] R1(config)# *Mar 1 00:01:47.247: %SSH-5-ENABLED: SSH 1.99 has been enabled R1(config)# *Mar 1 00:01:47.331: %PKI-4-NOAUTOSAVE: Configuration was modified. Issue "write memory" to save new certificate R1(config)#ip http authentication local R1(config)#exit R1# *Mar 1 00:02:07.791: %SYS-5-CONFIG_I: Configured from console by console R1#copy run start Destination filename [startup-config]? Building configuration... [OK] R1#
Note
In this example I use ip http secure-server to enable HTTPS communication
between CCP and the device.
CCP also supports plain-HTTP communication, use ip http server in this
case.
Beware in this case that the communication between CCP and the device
transits in clear form over the network and can be potentially intercepted
or altered.
CCP initialization
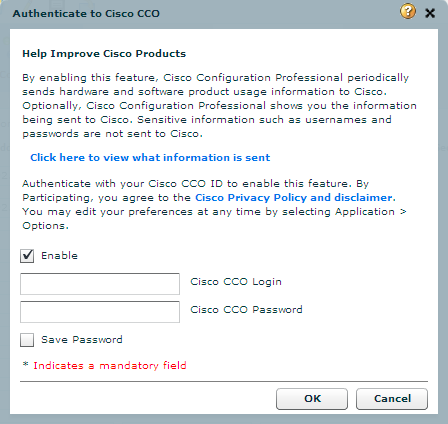
When you start CCP, you are first presented what looks like a login window:
Just clicking OK doesn’t work, my first reflex was to search to CCP default password. Actually, this window asks you for your Cisco Connection Online (CCO) credential, and is an optional step only to allow CCP to send usage reports to Cisco.
Just Cancel or untick the Enable checkbox.
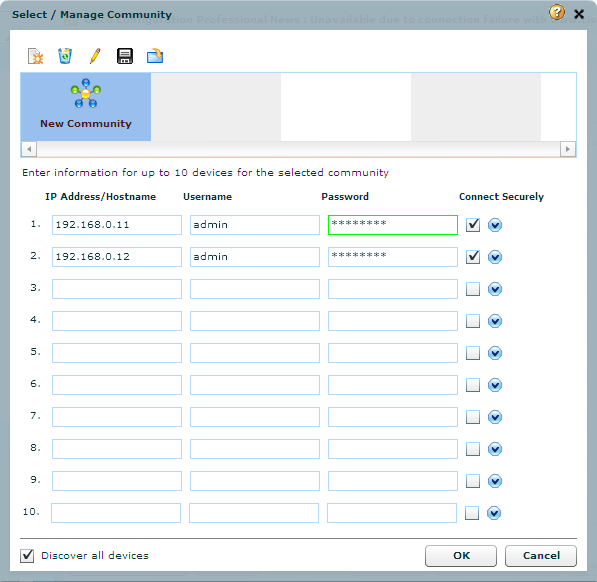
You are then asked for your devices IPs and credentials.
Filling this window is straightforward. Check the Connect Securely for devices where you enabled HTTPS.
Don’t forget to check the Discover all devices in the bottom left corner to automatically launch the discovery on all devices as soon as you press the OK button. If you forget to check it, this is not a big deal: on the next screen simply select your devices (use Ctrl or Shift to select several devices at once) and click on the Discover button at the bottom to manually launch the same operation.
Note
CCP does not store devices properties in its database. On each start you need it to discover them: CCP connects to the devices, detect their type and collect all relevant properties.
When using devices virtualized in GNS3 using common IOS images, you may have a “Discovered with warnings” status. Clicking on the Discovery details button usually tells that the warning is generated because the device is not supported by CCP and that some functionality may not behave as expected.
This is a normal message and personally I never encountered any odd behavior.
CCP “Express” 3.x
This one is more regularly maintained, nevertheless I did not managed to install it due to errors potentially related to the GNS3 virtualization environment.
The installation process is documented by Cisco, but it doesn’t work first because IOS fails to simultaneously read and write to its flash memory. To decompress the installation archive, you must therefore read it directly from the TFTP server instead of copying to the flash memory first:
R1# archive tar /xtract tftp://192.168.0.100/ccpexpressAdmin_3_1_2_en.tar flash:
However the installation process then fails on the following step due to too long file names:
Error opening flash:/ccpexp/CCPExpress_3.1_Open_Source_Documentation.html (File name too long)
According to the linked forum thread, these issues seem to be specific to GNS3 environment (maybe because of GNS3 itself, or maybe because using GNS3 usually means using old obsolete IOS images). In theory, you should not encounter such issues with real gears.
I did not investigate this any further yet.