In this article:
The five Ws
-
What: The EC-Council Certified Ethical Hacker (CEH) is a technical certification on penetration testing.
While being oriented toward technical people, the certification itself goes lightly on the practical side but insists instead on having a broad general culture. This certification covers definitions, concepts, tools, as well as a strong focus on ethic.
This certification never go really deep in any subject, but instead attempts to cover the widest possible range of topics related to pentesting. Example of covered topics include cryptography, regulation and compliance, operating systems (client, server and mobile systems are all covered), networking (including wireless networking), procedures, code review, physical security, social engineering and, last but not least, ethic.
-
When: This certification has no prerequisite (a two years experience in IT security allows to avoid the training requirement, but subscribing to an approved training removes any experience prerequisite).
It is suitable for anyone interested in computer security. People with really no prior knowledge on computer security may find themselves lost at first in the large number of topics covered by this certification. This just means that they will require more time to study, and progress step-by-step. With some efforts even fresh-beginners on the topic should be able to succeed.
-
Why: This certification demonstrates a strong general culture on penetration testing, the offensive side of IT security.
This certification however has little to no value in demonstrating practical abilities (on the other side more practical certification cannot cover such a wide range of subjects). This is not a problem for entry-level jobs where no practical experience is expected, however for more advanced level a complementary certification may be useful.
For US people, this certification is part of the list of the DoD 8570.01-M approved certifications, so it may open you some doors with some government entities or contractors. If you intend to use it just as a label on your resume, you may want to compare the cost of a CEH with other certifications: it may or may no be the best choice depending on your specific situation and needs.
-
Who: This certification is mostly useful for people entering the field of IT security and people regularly manipulating security-related tools or issues and wanting to deepen their knowledge from an offensive point-of-view.
-
People entering the field of IT security, either as a pentester or in another role, will obviously directly benefit from the general culture built by this certification.
People already with a few years of full-time work in the IT security field may not benefit the most from this certification. While it may help to fill some weaker areas, specialized certifications focusing on identified weaknesses may be a better investment.
-
People regularly manipulating security-related tools or issues, a typical example being system administrators, also benefit from this certification by gaining knowledge of the offensive side of IT security.
This is a topic which is rarely covered in usual system and network security certifications, but is mandatory in my opinion to have a sane approach of security and risk evaluation.
As Sun Tzu once wrote:
If you know your enemies and know yourself, you will not be imperiled in a hundred battles… if you do not know your enemies nor yourself, you will be imperiled in every single battle.
I just feel sorry for all those system administrators and IT managers who rely solely on vendor’s marketing discourses to take their decisions. They may tend to spend sometimes huge amount of money and efforts on things which will only marginally improve their security posture, while leaving vulnerable entry points wide open either because they are less profitable to their vendors or because they are too specific to appear on automated security assessment dashboards.
This certification allows to get a more critical point-of-view on things that really matters in terms of security, and better challenge vendors to get the most out of their offerings.
-
-
Where: The CEH exam can be taken in any Pearson VUE or Prometric test center.
Note
If you cannot justify of more than two years of experience in IT security (and if you can, as stated above, you may want to double-check if this certification is indeed the most appropriate for you), you must subscribe to an official training to be eligible to take the exam.
See the mandatory training section below for more information.
The exam cost has considerably increased since I took it myself. The exam itself now costs around $1000 USD (since CEH v9, CEH v7 and v8 cost was $500), add to this a non-refundable eligibility application fee of $100), but all this is usually bundled in the price of the nearly-mandatory training you must take. All people certified after January 1st 2016 must also pay a $80 annual membership fee to keep their certification.
The exam itself is composed of 125 multiple-choice questions you must fill in 4 hours.
Warning
The exam condition varies depending on where you take the exam. See the examnation process section for more information.
Training material
Building a lab
If you already are familiar with offensive security, then you will need little to no practice for this exam. Personally my only practice was for the OSINT-part which presented me new tools and techniques, but this is a very minor point and took, all-in-all, a single-afternoon.
The EC-Council provides you as part of the official courseware a huge archive containing 40 GB of Windows software (6 DVDs for the disc-based version). Personally I never used them and have no use for them either (well, there was a 3 minutes video about Kevin Mitnick, this was the only file usable on my Linux box and that I bothered to open). Even if I need to work on a Windows machine, I think I would prefer to download the latest version of a given software directly form the project website than using a potentially outdated version from such archives.
Nevertheless, people not familiar with offensive security will find in the CEH curriculum a mater to a lot of practical exercises as numerous tools and techniques are mentioned in the curriculum. In such case, if nothing else the archive is at least a safe way to ensure that you have access to the software described in the course (even-though there is sadly not a 1:1 matching between the software mentioned in the course and the software available in the archive, and the software available in the archive may not be up-to-date).
Unless explicitly mentioned, the CEH exam won’t test you on any advanced feature of the mentioned tools. What is important is to know their name, when and how they are most commonly used and how they work internally at a high level. Corner cases are usually out-of-topic.
Learning resources
As stated in the CEH eligibility criteria, if you cannot justify of more than two years of professional experience in an IT security job, you must must buy training from an EC-Council partner to be eligible to take the exam.
Note
Buying the EC-Council official courseware does not count as an official training. The eligibility criteria page may seem confusing about this, but this is (a bit more) clearly stated in the courseware page (emphasize is mine):
Exam voucher is not included. Students must apply for eligibility before purchasing exam voucher. Please check the eligibility criteria
This is not a question about your current skills and knowledge, this is not a question about your sense of organization allowing you to reliably self-study from books. In my opinion this is a question of business: it is the way for the EC-Council to bring guaranteed customers (and money) to its partners training companies.
Fortunately, several companies provide affordable e-learning courses that satisfy these prerequisites. So the most affordable route to the CEH exam is to study from books as you would do for any other exam, and then subscribe to such e-learning courses to satisfy the exam eligibility conditions.
Note
E-learning offers often go by period. Self-learning on your side before starting the e-learning program allows you to ensure that you won’t need to renew or buy training time extensions which may often be very expensive.
I suspect that some training provider have a business model where they sell one-month (for instance) e-learning training session at a very low price to attract customers, with the assumption that no student will never be able go through the whole EC-Council curriculum in such a low time, so they will be able to fund themselves by selling overpriced time extensions.
A CEH exam is very expensive when you have to pay it from your own pocket (even more now, personally I’m even not sure I would do it now), so you may want to act wisely.
Self-study
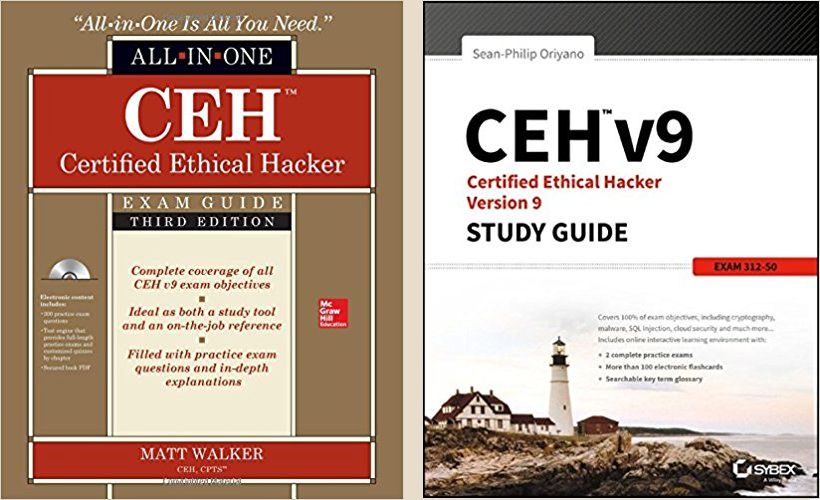
The books by Matt Walker (All-in-One series) and Sean-Philip Oriyano (Sybex) are safe values for your studies. I recommend buying both as they complement well each other. Which one you will use as your primary study material is left to your choosing.
Personally I passed more time with Matt’s book as it is written in a more enjoyable style, with personal anecdotes scattered throughout the book.
Sean-Philip however goes more deeper in background information, which come particularly handy on areas where Matt’s book may be lighter (like cryptography or wireless networks), but Matt provides some information missing in Sean-Philip’s book. Moreover, having two books is useful when you want to double-check an “EC-Council approved” definition.
Warning
Beware of technical terms and definitions when studying for the CEH exam. Some may more reflect EC-Council‘s own opinion on a specific matter than a universally accepted position.
In such cases the CEH exam is not about what you think. It is testing whether or not you know EC-Council‘s own position on the matter.
The books mentioned here are well written and do not refrain from highlighting such discrepancies between the CEH curriculum and the usual field practices. They ultimate goal is indeed not to make you become certified but to make you become a reliable professional.
Matt’s book is also provided with a free .pdf version of the book. I found it specially useful to quickly search throughout the book from any random term.
Now both are also available in bundled versions providing more exam-like questions (see here and there). When I passed my exam only Matt’s book proposed this and I took advantage of this and was happy with the questions. However, depending on the mandatory training offer you will subscribe, this may be optional.
Books’ questions do a great job in allowing you to thoroughly test your knowledge and detect weak areas, but they are not actual EC-Council‘s questions. I strongly recommend to also get your hands on questions from old exams, depending on the formula you subscribe you may get them as part of your mandatory training (after having signed a non-disclosure agreement, of course). They will help to prepare yourself to better handle EC-Council‘s sometimes odd questions and phrasing.
Note
Also fetch a book on Metasploit. I would recommend it even if you already know how to use it: a lot of people only know the feature they commonly use and ignore the existence of certain other features.
Matt only very briefly presents it, Sean-Philip doesn’t even mention it (according to the index), and you will most likely get questions on it in your exam (mainly about features and names).
I bought Mastering Metasploit by Nipun Jaswal which provides a good introduction on everything you need to know on Metasploit, but other book may also be fine.
As with anything else, there is no requirement of any practical experience with Metasploit to pass the exam so simply reading the book once should be sufficient.
Mandatory training
The cheapest EC-Council approved training formulas may be quite barebone. As with any official training, you will be provided with:
- The 40 GB archive of Windows software I mentioned in the building a lab section.
- A set of more than 2000 slides in .pdf files (in fact DRM-protected 1-year limited .pdf files readable only on Windows hosts allowing connections to a non-standard, potentially firewalled port to EC-Council servers to validate your right to open the file). While these files may be usable very occasionally to confirm EC-Council‘s official position on certain topics, I consider them unusable for self-learning.
Depending on your formula, you may also have access to some kind of forum or chat to ask questions to a trainer, and you may also have an option to get access to exam-like questions.
Note
If your e-learning formula proposes exam questions as an option and at a reasonable price, seriously consider subscribing to it as it may be a very good investment.
CEH questions and expected answers may sometimes seem… odd. Official training partners usually have access to genuine CEH questions from past exams protected behind a NDA.
These exam questions was the highest value I got from my mandatory training, and these questions helped me far more than the questions available in published books (they are good to test your knowledge, less good to prepare you against EC-Council‘s specific tricks).
When choosing a training, you must make sure:
-
That it is an official training counting as a replacement for the two years of experience requirement. Don’t assume it as some training providers may use ambiguous marketing buzzwords and logos but contact them and check this explicitly.
-
Check whether or not the exam voucher is included in the training price. Either way is good, but the exam voucher alone is around $1000 USD so you must take this into account when comparing training prices from different providers.
Personal impressions
Curriculum
CEH curriculum is very wide, and successfully allows to build a general culture in a large number of domains.
It is light regarding practical training but I think this is intended and, as long as it is expected, I don’t consider this a negative point:
-
The curriculum is designed to teach a body of knowledge not only for actual pentesters but also for people more remotely involved with IT security like system administrators for instance.
People planning to become pentester usually already have a practical knowledge that system administrators (to keep the same example) may not have. I therefore consider it normal that they may consider this certification to be weak from a practical point-of-view: it simply targets a more wider audience than pure IT security experts.
-
Due to the wide range of domains covered, entering into the details of each domain would make the CEH curriculum size grow exponentially while answering no real need as no one needs a detailed knowledge of everything.
This certification provides a strong general culture. When a topic requires further digging, more closely study can be done as the need comes either as part of a personal technology watch or as part of another, more focused certification.
This certification has a strong focus on learning definitions and software names. While I understand the need of definitions to establish a common language, and the need of software names to be able to invoke the right tool for a given task, the CEH curriculum pushes this either too far or not enough, I don’t know, but the software names part in particular left me a very uncomfortable feeling.
-
Either there is a list of software that any security professional is meant to know. In such case, the EC-Council should publish this list as part of the CEH curriculum.
Currently the names of several hundred tools and websites (URLs) is mentioned, most often only once and given in an informal example, scattered over the 2000+ official slides. However, each tool and website name may be equally testable. I don’t see how one is expected to study this.
The EC-Council should publish a standalone index of well-known security tools and reference websites. This would both make studying easier, and allow the EC-Council to put a stronger focus on the tools and information sources that they consider essential for the profession.
This would be a win-win.
-
Otherwise questions about software and sites names should be made less frequent to get less weight on the final score.
I passed the CISSP exam too, another certification which follows a similar “general culture” goal than the CEH. The CISSP also mentions some tools and websites as part of the curriculum, but very few so our attention can remain focused on actionable information, and there are really few questions about such names during the exam as this is not considered a major knowledge.
Simply knowing a set of names doesn’t make you a greater practitioner in field.
Exam
Questions quality
While for all the other certifications I covered until now I always began this section by stating “the question are clear and non-ambiguous”, I won’t do this here.
A noticeable amount of CEH exams questions are definitively unclear, ambiguous, out-of-nowhere or the expected answer may be dubious if not plain wrong (see this example). Expect to loose 10-15% of your total score on such questions: as it is random is may be less, but it shouldn’t be more.
While being a significant number, this shouldn’t however prevent you from successfully passing the exam, just don’t expect to ever reach 100% either in realistic trainings or in the final exam. While in training just ensure that you consistently get at least 85% of right answers, and you should be fine for the final exam.
Examination process
The examination process varies depending on the location where you pass the exam:
-
Prometric test centers deliver exams in similar condition than common trainings: 125 questions, 4 hours, with the possibility to review previous questions at any time.
-
Pearson VUE test centers divide the exam in several sections, following the CEH Blueprint sections. The sections come in random orders.
The 4 hours time is divided between these sections proportionally to the number of questions, the shortest time is for the Ethics section where the three questions must be answered in less than 5 minutes (it is really scary when you are not prepared to this! Moreover EC-Council “ethic” questions may be really confusing at times…).
To not arrange anything, the time not used for a previous section is not added to the following section. Let’s say that you had 30 minutes left in a section and the next one will be the Ethics one, the timer still starts at 5 minutes, in bold orange warning mode.
At last, while you can review previous questions from the current section, you cannot review previously validated sections. Each section behaves as an individual exam.
Needless to say that the Pearson VUE examination process is far more stressful and less convenient than the Prometric one, in particular when you are not expecting this (I didn’t find this documented anywhere) and are wondering during the whole exam if you are facing a bug of if it is normal (and it is indeed “normal”, one of the many surprises awaiting the CEH students ;) !).
At least, dear reader, you are now warned and can now prepare yourself !
Conclusion
The EC-Council heavily relies on marketing:
-
Their website is stuffed with buzzwords: open-source security tools become “Underground Hacking Tools”, a virtual lab becomes a “Cyber range”, and of course the entry-level CEH certification is described as:
The Certified Ethical Hacker program is the pinnacle of the most desired information security training program any information security professional will ever want to be in.
-
Preparing for the exam is very expensive, with an ingenious system to push students to training centers.
When I passed my certification prices were far lower than they are now (voucher price increased by 100%, just WTF?) and no annual fee was required. Personally I’m not sure I would do it in the current conditions, at least not from my own pocket.
-
Their students resources is protected with a highly demonstrative security.
The website is protected using mandatory two-factor authentication. Well, in fact a one-time code is sent upon each connection attempt to your mailbox, but this is indeed two-factor, isn’t it? And despite being bothering to use at least it significantly improves security, doesn’t it?
And once connected to your student area you can download their slides as DRM-protected .pdf files requiring a Windows host and an update of your firewall rules to be opened. But these files must be very precious to be so carefully protected!
-
The learning material seems both very classy, very impressive, and very useless.
I still don’t know what to do with their six DVDs full of Windows hAx0r 1337 stuffz (whoops, sorry, “Underground Hacking Tools”). Their 2000+ slides also are all very eye-candy, crafted by professional graphic designers, very colorful with a lot of graphical effects and so on… all this making them completely unusable for a proper learning experience where the medium must not be distracting to the student.
-
Once you passed the exam, you very regularly receive ads for paid events organized by the EC-Council (but rest easy, you benefit from “exclusive” reductions reserved to the elite people you now belong to!).
“dazzling the masses with bauble”, as he said…
Nevertheless, EC-Council marketing is also dual-sided: while they are trying to sell things to you, they are also selling the certification to companies which is good thing as this is those company which will then want to hire CEH people like you. EC-Council marketing power therefore also benefits to you.
Doing abstraction from these various money making techniques, I still believe the content of the curriculum to be interesting. This certification was indeed the occasion to cover domains that wasn’t covered by any of the other certs I took until now. However, again, the latest price increase may now make it less interesting for self-learners.